Ethical Hacking! An action performed by a hacker to malfunction a system or an entire network with an intention to interrupt or crash the framework bypassing all the security issues such as a strong password set by the owner of the Network. Whereas a company look into this technique in a different way i.e; the companies uses these strategies in order to increase their security in a hacker point of view. This is what you will be learning at our ethical hacking course in Vellore. The training offered here will make you face the obstacles that are posted in the real time hacking industries.
According to an old saying “Be a roman, when you are in roman”, to become an ethical hacker you should turn in to one. The demand for ethical hacker is increasing worldwide, though it is the highest paid job in India as well as abroad. Unhappily there are less number of ethical hackers are available to fill out the opened positions in leading companies in the world. Our ethical hacking course would act as a gateway for you to enter in to a reputed concern. For this all you have to do is to join Redback Academy and pursue your ethical hacking training.
Our procedure lies in training our students in all the perspective that a professional hacker would thick. Since our trainers are present employees of foremost hacking companies, they would give you real time training on how to hack tiny network. Through which you will be gaining the knowledge of how to face an actual work environment. This includes, understanding the tools required for hacking and pace of environment where all the action will be held. These are our talent that we are implementing in teaching hacking course in Vellore for a long time.
Our teaching would be completely a practical one, with minimal number of theory classes. Students are allowed to take advantage of our Lab facility at the time we are opened. We do provide an International certification to our students on successful completion of the training and that would be from EC council. You can contact us at any time for a free demo class to get an in depth knowledge about the course that you are about to learn. We are ready to help you with all our effort to make you a ethical hacker as soon as possible. Don’t just wait anymore, call us now to enroll for the course.
Ethical Hacking Course Syllabus:
- Introduction to Ethical Hacking
- Footprinting and Reconnaissance
- Scanning Networks
- Enumeration
- System Hacking
- Trojans and Backdoors
- Viruses and Worms
- Sniffers
- Social Engineering
- Denial of Service
- Session Hijacking
- Hacking Webservers
- Hacking Web Applications
- SQL Injection
- Hacking Wireless Networks
- Hacking Mobile Platforms
- Evading IDS, Firewalls, and Honeypots
- Buffer Overflow
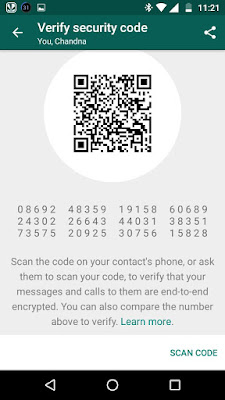
- Cryptography
- Penetration Testing
Why Ethical Hacking Course in Vellore at Redbakacademy?
- We provide innovative and practical teaching methods in attempt to make learning more interactive.
- We are open 7 days a week. You can enjoy the flexibility of weekday and weekend schedules based on your convenience.
- At the end of the course, each student will be assigned with mini project. In addition, we also give the opportunity of working in real time projects based on their ability.
- Our training institute is facilitated with high-end infrastructure and lab facility.
- Intensive training through certified by ethical hackers working in leading MNCs
- In depth subject coverage and excellent training
- We also offer 100% placement assistance to our students to make impressive presence in reputed web design industries.
Looking for best Ethical Hacking Training Course in Chennai? Enroll in FITA. Get Trained by Certified Ethical Hacker and become one!
Related search terms: Ethical hacking course in Vellore, kanchipuram, Chittor, Gudiyatham, Chennai, Ethical hacking course, Hacking course in Vellore, kanchipuram, Chittor, Gudiyatham, Chennai, Ethical hacker course in Vellore, kanchipuram, Chittor, Gudiyatham,Chennai, Ethical hacking training in Chennai, Ethical hacker training in Chennai, Ethical hacking course in Vellore, kanchipuram, Chittor, Gudiyatham,Chennai, Best ethical hacking institute in Vellore,kanchipuram, Chittor, Gudiyatham,Chennai, Ethical hacking training center in Vellore, kanchipuram,Chittor, Gudiyatham,Chennai, Ethical hacking training institutes in Vellore,kanchipuram,Chittor,Gudiyatham,Chennai, Ethical Hacking Course in Vellore,kanchipuram,Chittor,Gudiyatham,Chennai, Ethical Hacking Course in Chennai, Ethical Hacking Course in vellore.